Most creators assume image theft is a problem reserved for celebrities with millions of followers. That assumption is dangerously wrong. 73% of creators with more than 100k followers have experienced harassment or privacy violations, and 34% of those cases escalated into real-world threats. Whether you're building a lifestyle brand or managing multiple accounts for clients, your images are your business assets, and leaving them unprotected is like leaving your studio unlocked overnight.
Table of Contents
- The main threats: why image protection matters more in 2026
- How influencers protect their images: core methods and tools
- Privacy and safety: metadata and doxxing risks for creators
- Brand value and licensing: protecting your aesthetic and IP
- The uncomfortable truth about influencer image protection
- Take control with untraceable image solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Image misuse is common | Most influencers face risks like copyright theft, AI abuse, and privacy violations. |
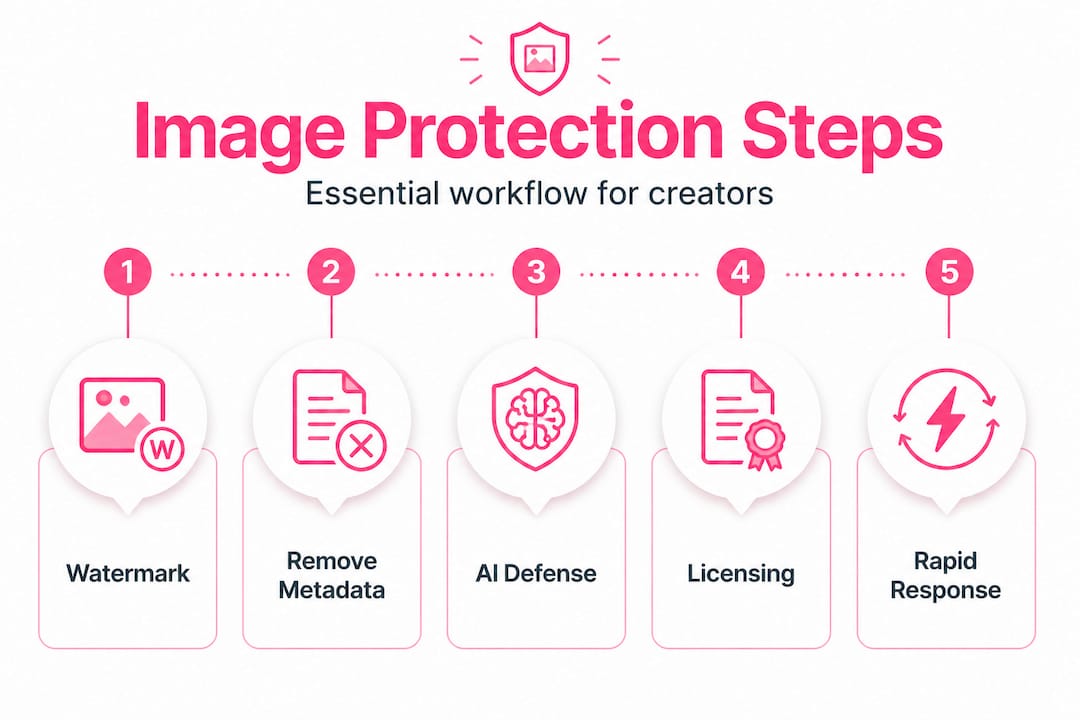
| Protection uses layers | Combining watermarks, metadata management, and specialized tools offers the strongest defense. |
| Metadata removal aids privacy | Stripping location or device data from images can prevent doxxing and stalking. |
| Your brand is your IP | Controlling image use through licensing protects and monetizes your unique aesthetic. |
| No method is foolproof | Risk reduction, not total elimination, is the goal for influencer image protection. |
The main threats: why image protection matters more in 2026
Let's be clear about what's actually at stake. Image protection isn't just about someone reposting your photo without credit. The threat landscape has grown significantly more complex over the last few years, and understanding it is the first step toward building real defenses.
There are four major threat categories every creator should know:
| Threat | Consequence | Real-world scenario |
|---|---|---|
| Copyright infringement | Lost revenue, brand damage | A competitor reposts your styled shoot and monetizes it |
| AI misuse and deepfakes | Reputation harm, nonconsensual content | Your face is used to generate fake explicit images |
| Privacy violations and doxxing | Physical danger, stalking | EXIF data reveals your home location to a bad actor |
| Brand dilution | Reduced commercial value | A brand uses your aesthetic without permission or payment |
Influencers protect images primarily to prevent copyright infringement and unauthorized commercial use. Watermarks and metadata serve as the first line of legal defense. But copyright is only one piece of the problem. AI misuse is the fastest-growing threat in 2026, with bad actors using publicly available images for deepfake creation and training generative models without consent. Protecting against AI misuse now requires a combination of visible watermarks, invisible digital fingerprints, and newer tools designed specifically to disrupt AI scraping.
Here's what can go wrong when images aren't actively protected:
- Your photos get reposted by accounts with larger followings who gain followers and brand deals you should have received
- A brand uses your visual style in an ad campaign without licensing it from you
- A deepfake video is created using your face and shared without your consent
- Your location or home address is extracted from image metadata
- Sponsored content you created appears on unauthorized platforms, violating your brand contracts
The harassment angle is worth calling out directly:
"73% of creators with over 100,000 followers have experienced some form of harassment or privacy violation, with 34% reporting that those violations escalated into real-world threats."
Most image theft is opportunistic. Thieves and bad actors look for easy targets. Creators who take even moderate steps to protect their content make themselves much harder targets. You don't need perfect security. You need enough friction to push opportunistic thieves toward easier prey. Pairing good social media security tips with solid image protection habits creates a meaningful layer of practical defense. This also matters for protecting content IP as a long-term business asset, not just a short-term safety measure.
How influencers protect their images: core methods and tools
There's no single method that handles every threat. Effective protection means combining several tools and practices into a layered strategy. Here's how the main options compare:
| Method | Best use case | Pros | Cons |
|---|---|---|---|
| Visible watermarks | Deterrence and ownership proof | Recognizable, legally useful | Can be cropped or removed |
| Invisible fingerprints | Tracking unauthorized use | Hard to detect or remove | Requires specialized tools to verify |
| C2PA metadata | Content authenticity verification | Industry standard, verifiable | Platforms may strip it on upload |
| Glaze / Nightshade | Blocking AI training data scraping | Effective against AI models | Minimal visual protection for humans |
Watermarks and metadata establish ownership and are the foundation of any DMCA takedown process. Without them, proving your image was stolen becomes significantly harder. Invisible fingerprinting takes this further by embedding a unique identifier that survives compression and minor edits, allowing you to track where your image ends up even if the visible watermark is removed.

AI tools like Glaze and Nightshade work differently. Glaze adds subtle pixel-level changes to images that fool AI models into misidentifying your style. Nightshade goes further by "poisoning" training data, causing AI models that ingest your images to produce distorted outputs. These tools are especially relevant for illustrators and photographers whose distinctive styles are prime targets for AI scraping and imitation.
Here are the key steps to protect an image before posting it:
- Add a visible watermark with your handle or logo in a position that makes cropping difficult without destroying the image composition
- Embed invisible metadata fingerprints using tools like Digimarc or similar services to create a traceable ownership trail
- Strip your personal EXIF data to remove GPS coordinates, device info, and timestamps before uploading to any platform
- Apply Glaze or Nightshade if your visual style is distinctive enough to be targeted for AI training
- Register valuable images with the U.S. Copyright Office so you can pursue statutory damages if infringement occurs
- Run reverse image searches periodically using Google Images or TinEye to catch unauthorized use early
Pro Tip: Watermark opacity is a real tension point. Too transparent and it's easy to remove digitally. Too bold and it detracts from the image's commercial appeal. A good rule of thumb is 30 to 50% opacity placed strategically in an area that's integral to the image composition, not floating in a corner where it can be cropped out.
Safe image anonymization adds another layer by removing the private data embedded in every image file before it reaches a platform's servers. Pairing this with solid account security strategies ensures both your content and your accounts stay harder to compromise. Staying current with media production innovation also keeps you ahead of emerging threats and new defensive tools entering the market.
Privacy and safety: metadata and doxxing risks for creators
Every image you take with a smartphone or camera stores far more data than most people realize. This embedded data is called EXIF data (Exchangeable Image File Format), and it can include your GPS coordinates at the time of capture, the make and model of your device, the exact timestamp, camera settings, and sometimes even your device's serial number.
Stripping metadata before sharing images is one of the most effective ways to prevent stalking, doxxing, and location-based harassment. Doxxing occurs when someone collects and publishes private identifying information about a person online. For influencers, an image taken at home can reveal an exact home address to anyone who downloads the file and checks its metadata.
The privacy risks from unstripped metadata include:
- GPS location tracking: A single photo can confirm your exact home, gym, or school location
- Device fingerprinting: Consistent device metadata can link accounts you intended to keep separate
- Routine pattern mapping: Timestamps reveal when and where you're most active, which a stalker can exploit
- Harassment escalation: Location data transforms online harassment into a potential physical threat
Tools for removing metadata before sharing:
- ExifTool: A free, powerful command-line tool for stripping or editing any EXIF data
- Adobe Lightroom and Photoshop: Export settings include options to exclude location and device metadata
- Preview on Mac: A simple way to view and selectively remove metadata before export
- Dedicated apps like Metapho or ViewExif on iOS for quick mobile metadata management
Pro Tip: Don't assume platforms handle this for you. Instagram strips some metadata on upload, but it's inconsistent and depends on the file format. Always strip metadata yourself before uploading rather than relying on a platform's behavior, which can change without notice.
You can remove metadata from images efficiently using tools built specifically for content creators who need to do this at scale without disrupting their posting workflow. For a more complete approach, untraceable image solutions combine metadata removal with image variation to protect your privacy across multiple platforms simultaneously.
Be especially careful with images that show recognizable landmarks near your home, reflective surfaces that reveal location details, or consistent backdrops that let dedicated followers triangulate where you live over time. Privacy isn't just about the file, it's about the visual content itself.
Brand value and licensing: protecting your aesthetic and IP
Your visual style is not just a creative preference. It's a business asset. A consistent aesthetic builds audience recognition, drives brand partnerships, and creates measurable commercial value. When that aesthetic is copied or diluted without your permission, you lose real money and competitive positioning.
Images form core IP for influencers, and licensing control is the mechanism that prevents others from diluting that value. Copyright law protects individual images as creative works, but protecting a broader aesthetic is significantly more difficult legally. You can't copyright a "moody warm-toned food photo" style, but you can copyright specific images and pursue damages when those images are used without authorization.
"Protecting an influencer's visual aesthetic requires a combination of copyright registration, licensing agreements, and active monitoring, because courts have rarely recognized aesthetic style as protectable on its own."
Here are the key steps for maintaining licensing control over your image assets:
- Register your most valuable images with the U.S. Copyright Office to qualify for statutory damages in infringement cases
- Draft clear licensing agreements that specify permitted uses, platforms, duration, and geographic scope whenever you grant a brand permission to use your content
- Include takedown provisions in every brand contract that allow you to revoke permission if usage exceeds agreed terms
- Set up Google Alerts and reverse image search monitoring for your most-used images to catch unauthorized use quickly
- Document your creative process with timestamps and drafts to establish priority in any ownership dispute
Cases where image misuse has caused real brand harm are well documented. Influencers have discovered their photos used in ads for competing brands, their filtered aesthetics copied wholesale by new accounts, and their sponsored content repurposed without authorization in ways that violated their original brand deals. Each of these outcomes reduces the creator's perceived exclusivity and commercial value. Brands pay premiums for unique reach and distinct visual identities. When those get diluted, negotiations get harder and rates drop. Strong media production for brand ROI strategy treats every image as a protected asset from creation through distribution.
The uncomfortable truth about influencer image protection
Here's something most guides won't say directly: no protection method is foolproof. Someone determined enough will find a way around watermarks, metadata removal, and even AI-disruption tools. That's not a reason to give up. It's a reason to reframe the goal.
The actual objective of image protection isn't total security. It's risk reduction and rapid response capability. Most bad actors are opportunistic. They're looking for content that requires no effort to steal or repurpose. When you add even moderate friction through watermarks, metadata removal, and copyright registration, you eliminate yourself from the lowest-effort target category. That matters more than people think.
Legal tools like DMCA takedowns work best when combined with practical barriers. A watermark on its own won't stop a determined thief, but it makes your takedown case ironclad. A copyright registration alone won't prevent scraping, but it unlocks statutory damages that make pursuing the case financially worthwhile. The combination is what creates real protection.
Another truth: fear of theft shouldn't stop you from sharing content. The creators who disappear from platforms to "protect their work" lose the audience and revenue that make protection worth pursuing in the first place. The answer isn't to post less. It's to post smarter, with deeper anonymization strategies built into your workflow from the start.
The threat environment will keep evolving. AI misuse methods are advancing faster than defensive tools. New scraping techniques emerge constantly. This means your approach to protection can't be a one-time setup. It has to be a living practice you review and update as the landscape changes. The creators who handle this best treat it like platform algorithm literacy: something they stay current on because it directly affects their business. Proactive, educated sharing beats reactive crisis management every single time.
Take control with untraceable image solutions
Everything covered in this guide, from metadata removal to watermarking, AI protection, and privacy management, requires consistent execution across every image you post. That's a lot to manage manually, especially when you're posting at scale across multiple platforms and accounts.
One2Many.pics gives you a streamlined way to put all of this into practice. The platform removes metadata automatically, generates unique visual variations of your images to avoid duplicate content detection, and helps you post across accounts without leaving a traceable digital footprint. Whether you're an individual creator protecting your privacy or a social media manager handling bulk content for multiple clients, the tools are built specifically for the workflows you already use. You can even partner with One2Many.pics through their affiliate program to earn while helping other creators protect their content.
Frequently asked questions
How do watermarks help protect influencer images?
Watermarks visually assert ownership, making theft more obvious and legally defensible. They also support DMCA takedown notices by establishing clear proof of original authorship, as watermarks assist in ownership claims and force removal of infringing content when filed correctly.
Does removing metadata prevent stalking from social media images?
Yes. Stripping metadata before sharing removes GPS coordinates and device identifiers, significantly reducing the risk of location-based stalking or doxxing from image files.
What is the best way to stop AI from misusing influencer images?
Use tools like Glaze or Nightshade combined with visible watermarks to disrupt AI scraping. Protection against AI misuse requires layered defenses including invisible fingerprints and C2PA metadata standards for maximum effectiveness.
Why is licensing important for influencer images?
Licensing gives you documented control over exactly how your visuals are used and by whom. Without it, brand and aesthetic protection becomes nearly impossible to enforce, leaving your most valuable creative assets open to unauthorized commercial use.
