Over 90% of users carry a unique browser fingerprint that social media platforms can read instantly, even after you log out or switch to incognito mode. For influencers and content creators managing multiple accounts, that invisible signature can quietly tank your reach, trigger a shadowban, or get accounts flagged before you post a single piece of content. Logouts and cookie clears don't erase the fingerprint. Your device, browser settings, and posting behavior keep talking long after you think you've gone quiet. This guide breaks down exactly what social media fingerprinting is, how platforms build and use these profiles, and the concrete steps you can take to protect your accounts from suppression.
Table of Contents
- What is a social media fingerprint?
- How social media fingerprints are created
- Why platforms use fingerprinting and its effects on creators
- Strategies for protecting your social media fingerprint
- What most creators miss about social media fingerprinting
- Protect your content and grow your reach with one2many.pics
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Fingerprints persist | Social media fingerprints identify you across logouts and cookie clears. |
| Suppression risks | Managing multiple accounts from the same device can trigger shadowbans. |
| Consistent profiles matter | Keep device, browser, and behavior consistent to avoid detection. |
| Behavior is key | Adjust your engagement and posting habits to reduce tracking risk. |
| Practical tools exist | Anti-detect browsers and proxies help minimize your digital footprint. |
What is a social media fingerprint?
Now that you're aware every move online leaves a trace, let's clarify what a social media fingerprint actually is and why it's so powerful.
Think of your social media fingerprint as the digital equivalent of a physical fingerprint. No two are exactly alike, and the platform doesn't need your name or email address to recognize you. It just needs the combination of signals your device and behavior leave behind every single time you connect.
Social media fingerprinting is a tracking technique where platforms collect unique device, browser, and behavioral characteristics to create persistent identifiers for users, enabling detection of multi-account usage, bots, and policy violations leading to content suppression like shadowbans.
In plain terms: platforms are quietly building a profile of you that goes far beyond your username or IP address. Every device you use, every browser setting you carry, and every pattern in how you engage with content contributes to a signature that follows you around the internet.
For creators who are managing multiple accounts, working with brand partnerships, or simply trying to keep personal and professional content separate, this creates a real and underestimated risk. Platforms like Instagram, TikTok, and YouTube are actively using these signatures to detect what they call "inauthentic behavior," which often means flagging creators who run multiple profiles from the same setup.
Here's what that looks like in practice. You log into Account A on your laptop at 9 a.m. to post a brand collaboration. Later that afternoon, you switch to Account B on the same device to manage a side project. The platform's system already recognizes the fingerprint match and starts treating both accounts as linked. Neither account has broken any rules explicitly, but both are now at elevated risk for reduced reach, content suppression, or outright restriction.
The part that catches most creators off guard is the persistence of fingerprints. Deleting the app, clearing cookies, or using a different browser tab does nothing to erase your device-level signature. A solid social media security guide always starts with understanding this reality before moving on to solutions.
Key reasons why fingerprinting matters for creators:
- Your accounts can be linked without any shared login credentials
- Content suppression can happen silently, with no notification from the platform
- Fingerprints persist across sessions, devices, and even VPN changes if hardware signals are shared
- The more accounts you manage from one device, the stronger the connection platforms see
- Understanding the privacy protection impact of fingerprinting is the first step toward reclaiming control of your content's reach
Fingerprinting isn't a niche concern for hackers or data scientists. It's a frontline issue for every creator who takes their content strategy seriously.
How social media fingerprints are created
With a definition in place, let's uncover exactly how your social media fingerprint is assembled every time you log in or post.
The fingerprint isn't built from one data point. It's assembled from dozens of signals that are combined into a profile that is statistically unique to you. There are three main categories: browser fingerprinting, device fingerprinting, and behavioral fingerprinting. Each one contributes its own layer.
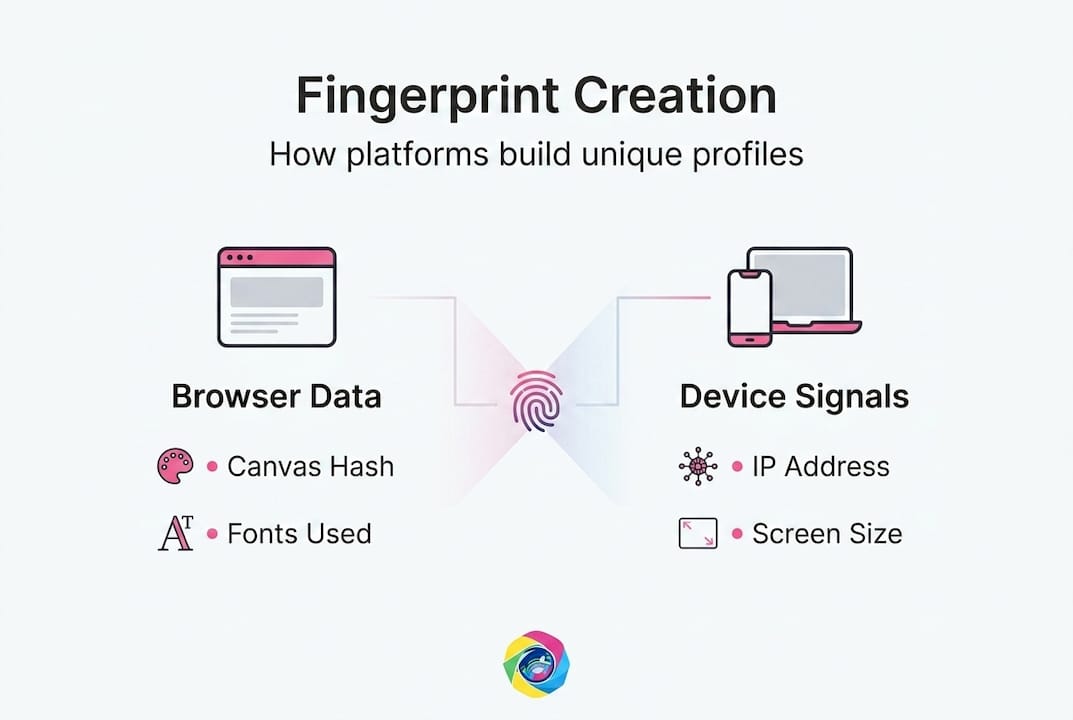
Key mechanics include browser fingerprinting (canvas hashing, WebGL rendering, fonts, screen resolution, user agent, timezone), device fingerprinting (IMEI, OS version, hardware IDs), and behavioral fingerprinting (posting patterns, engagement timing, navigation habits).
| Fingerprint type | Data collected | Risk level |
|---|---|---|
| Browser | Canvas hash, fonts, screen size, timezone, user agent | High |
| Device | OS version, IMEI, hardware IDs, battery status | Very high |
| Behavioral | Posting schedule, engagement timing, scroll speed | High |
| Network | IP address, ISP, connection type | Medium |
Here's how the assembly process actually works, step by step:
- Canvas fingerprinting renders an invisible image in your browser. The way your GPU and fonts process that image creates a hash that is specific to your hardware and software combination.
- WebGL rendering tests your graphics card's response to a specific 3D rendering task. Every GPU produces a slightly different output.
- Font enumeration detects which fonts are installed on your system. Rare font combinations narrow identification significantly.
- Screen resolution and color depth contribute to the profile, especially when combined with device pixel ratio for Retina and high-DPI displays.
- Timezone and language settings help platforms cross-reference your claimed location with behavioral patterns.
- Behavioral signals are collected continuously. The time you typically post, how fast you scroll, how long you spend on each post, and even mouse movement speed all create a behavioral fingerprint on top of the device and browser layers.
The result is strikingly precise. Over 90% of users have unique browser fingerprints, meaning most people are instantly identifiable without any cookies or logins. This is not a theoretical vulnerability. It is the standard operating procedure for major platforms right now.

The social media's technical impact on communities and creators is significant partly because of how invisible this tracking is. Most creators assume that switching accounts means switching identities. The platform disagrees.
Pro Tip: Never run two accounts with the same combination of browser, timezone, and proxy. Even one matched signal significantly increases the risk of linking. Treat each account as if it belongs to a completely different person using a completely different device in a completely different city. Use dedicated account security basics for every profile you manage.
Why platforms use fingerprinting and its effects on creators
Understanding the technology leads to a new question: Why are platforms so invested in fingerprinting, and what real consequences do creators face?
Platforms have legitimate reasons to track fingerprints. Spam networks, bot farms, and coordinated inauthentic behavior are genuine problems. A single actor running thousands of fake accounts to inflate engagement metrics undermines the integrity of the entire platform. Fingerprinting is one of the most effective tools platforms have to detect and remove these bad actors at scale.
Platforms like Instagram and TikTok use these fingerprints to link multiple accounts from the same device or IP, triggering shadowbans or restrictions on content reach for influencers managing multiple profiles.
The problem is that the same system that catches bot operators also catches legitimate creators who manage multiple accounts for different clients, brands, or content categories. The algorithm doesn't distinguish between a spam farm and a freelance social media manager running five client accounts from a home office. Both look the same in the data.
| Scenario | Platform interpretation | Creator impact |
|---|---|---|
| Two accounts, same device | Linked multi-account | Suppressed reach on both |
| Same posting schedule, two accounts | Automated behavior | Flagged for review |
| Shared IP across accounts | Single-actor operation | Potential ban risk |
| Unique devices and proxies per account | Separate users | Normal treatment |
Privacy advocates see fingerprinting as surveillance evading GDPR consent, while platforms view it as necessary for fraud prevention and authentic content enforcement. That tension is real, and it has no clean resolution in the short term.
What actually triggers suppression? The patterns that raise flags the fastest include:
- Posting identical or near-identical content across accounts in quick succession
- Logging into multiple accounts from one device without any profile isolation
- Using the same image files across accounts without modification (including embedded metadata)
- Rapid follower growth patterns that look artificial
- Engagement timing that is too consistent or follows non-human rhythms
Learning how to anonymize images is one of the most underutilized strategies in this space. Metadata embedded in your image files, like GPS coordinates, device model, and timestamps, can contribute to fingerprint matching just as powerfully as browser signals.
The influence of behavioral fingerprinting on content visibility is growing, not shrinking. Platforms are investing more resources in behavioral analysis every year, which means the creators who understand and adapt to this reality will have a measurable advantage over those who don't.
Strategies for protecting your social media fingerprint
To stay one step ahead, creators need to shift from awareness to action. Here's how to safeguard your footprint and secure your content.
The most effective protection strategies work on all three fingerprinting layers simultaneously: browser, device, and behavioral. Addressing only one layer while leaving the others exposed gives you a false sense of security.
Anti-detect browsers like Multilogin and GoLogin create isolated profiles with consistent spoofed fingerprints, and pairing them with residential proxies per account is the current gold standard for multi-account management.
Here's a practical protection framework, built for creators managing multiple accounts:
- Assign one anti-detect browser profile per account. Each profile should have its own spoofed canvas hash, user agent, screen resolution, and timezone. Never reuse profiles across accounts.
- Pair each browser profile with a dedicated residential proxy. Residential proxies route your traffic through real home IP addresses in specific locations. Match the proxy location to the timezone in your browser profile.
- Stagger your posting schedules. Identical timing across accounts is a behavioral red flag. Even small variations in when you post, engage, and respond to comments reduce the behavioral correlation score.
- Scrub metadata from every image before uploading. Your camera's EXIF data includes device model, GPS location, and timestamp. Platforms can read this data and use it to link accounts that share device information.
- Warm up new accounts gradually. Inconsistent fingerprints and mismatched OS and font combinations flag as suspicious. New accounts that instantly post at full volume look automated. Spend the first week engaging naturally before ramping up content output.
- Never cross-contaminate profiles. Logging into Account B while Account A's browser profile is still active is one of the fastest ways to create a detectable link.
Pro Tip: Match every detail of your browser profile's timezone, language, and screen resolution to the residential proxy location you're using. A profile claiming to be in Los Angeles but connecting through a Chicago IP with Eastern Time system settings is a mismatch that platforms detect easily. Consistency across every signal is more important than making any single signal look perfect. Use comprehensive account security tips to build airtight account isolation from day one.
One critical mistake many creators make is relying too heavily on VPNs rather than residential proxies. VPNs share IP addresses across thousands of users and are commonly flagged by platform systems. Residential proxies, by contrast, look like regular home internet connections because they are regular home internet connections, just routed through a privacy-focused network.
What most creators miss about social media fingerprinting
Here's a perspective you won't find in most privacy checklists: the creators who get suppressed most often aren't the ones who skipped the technical setup. They're the ones who got the technical setup right but completely ignored their behavioral fingerprint.
You can run the cleanest anti-detect browser setup money can buy, use a different residential proxy for every account, and still get flagged because your posting rhythm across all five accounts is identical. Platforms don't just look at whether your devices match. They look at whether your behavior patterns match. And behavior is surprisingly hard to fake convincingly.
The irony is that too much randomization backfires. Creators who overcompensate by randomly varying every possible setting end up creating a fingerprint that looks unnaturally inconsistent. Real users are creatures of habit. They post at roughly similar times. They engage for roughly similar session lengths. They have recognizable content themes and tones. Mimicking that organic consistency is harder than it sounds, and it requires treating each account as a fully realized persona, not just a technical container.
Most creators treat privacy as a purely technical problem. It's actually a behavioral and strategic problem. The deeper security strategies that actually work long-term are the ones that build genuine account personas with distinct posting cadences, engagement styles, and even content aesthetics. The platforms aren't just looking for fingerprint matches. They're looking for behavioral anomalies. The goal isn't to disappear. It's to look convincingly like a real, individual human being who happens to be posting great content.
Protect your content and grow your reach with one2many.pics
Ready to take privacy beyond just browser tweaks? Here's your next step toward true digital autonomy.
One2many.pics is built specifically for creators who understand that fingerprint protection doesn't stop at the browser level. Your image files carry their own fingerprint in the form of metadata and visual patterns that platforms use to link accounts and detect duplicate content. One2many.pics strips that metadata, removes device and location identifiers, and generates visually unique versions of your images so each account gets content that looks and reads as completely original. Whether you're managing five client accounts or fifty, the platform scales with you. Explore the tools at one2many.pics and check out affiliate opportunities if you want to monetize your expertise in creator privacy while helping other influencers protect their reach.
Frequently asked questions
Can social media fingerprinting track me if I clear cookies or use incognito mode?
Yes, fingerprinting works independently of cookies and incognito mode because it reads device hardware, browser configuration, and behavioral signals that persist across sessions. Behavioral linking persists across discontinuities like cookie clears, making these common privacy steps ineffective against fingerprinting.
What triggers shadowbans related to fingerprints on Instagram or TikTok?
Running multiple accounts from the same device or with matching fingerprints is the most common trigger. Instagram and TikTok detect shared fingerprints that link multiple accounts from the same device or IP, resulting in suppressed reach, and shared fingerprints are one of the primary signals these platforms act on.
Is it possible to completely prevent fingerprinting on social media?
Complete prevention is practically impossible, but you can reduce your risk significantly. Anti-detect browsers like Multilogin and GoLogin with isolated profiles, residential proxies per account, and careful behavioral management bring your risk to a manageable level.
How unique is my browser or device fingerprint?
Extremely unique. Over 90% of users have a unique browser fingerprint, which means most devices are instantly identifiable to platforms without any login or cookie data required.
